The Guide to Kolide's Okta Integration
Earlier this year, we fundamentally changed how end users interact with Kolide. We integrated our agent with Okta, and made Kolide part of a user’s authentication process. Now, when devices are out of compliance, users can’t log into their Okta-protected cloud apps until they’ve resolved the issue.
This change has several implications for IT admins, end users, and Kolide itself.
- End users can no longer ignore device security problems–they have to fix them in order to do their jobs.
- IT teams can ensure the entire fleet gets compliant with no interventions from them, which is particularly important for urgent security issues like browser and OS patching.
- Kolide is now part of the Zero Trust space, since we now restrict access to sensitive resources based on device health.
So that’s the tl;dr, but we’re going to spend the rest of this blog digging into why we chose Okta and how the integration fits into Kolide’s product as a whole (since it’s not the only big change we’ve made)!
What Is Okta?
Okta is an Identity-as-a-Service (IDaaS) platform, which in turn is a subset of the Identity and Access Management (IAM) field. Okta provides organizations with a suite of powerful identity management features for their workforce. In particular, Okta offers SSO and MFA, which are at the heart of Kolide’s Device Trust model.
Why Kolide Integrated With Okta
At Kolide, we’ve known for a while that it’s not enough to simply nudge users to fix issues; there have to be consequences for devices that are out of compliance. (Our CEO, Jason, even wrote about this idea in Honest Security). Eventually, we realized that the best and least invasive way to ensure compliance is to make device security part of authentication. That, in turn, required us to work with an SSO provider.
We chose Okta because we truly value how much they have invested in their platform, as well as their impact in the SSO community. Okta has an intentionally narrow focus and is easier to use compared to similar solutions, and many of our existing customers were already Okta users.
These qualities made Okta our first choice for integration, however, we do plan on adding more, so if you’re not an Okta customer, stay tuned!
How Kolide Integrates With Okta
Kolide integrates with the newest version of Okta Identity Engine. What makes Okta Identity Engine different from traditional SSO providers is its ability to utilize custom authentication hooks at each step of the authentication and authorization process. Thus, it drives user behavior more effectively than traditional SSO methods.
In Okta’s authentication flow, Kolide’s agent functions as a possession factor. That is, the presence of Kolide’s agent on a device is a precondition for authentication, so only devices that possess Kolide and pass our compliance checks can log into their Okta-protected apps.
Kolide also ensures that only the registered device owner can authenticate. This means that phished credentials become a problem of the past. Without the physical work computer present, credentials alone won’t satisfy authentication.
- Okta Identity Engine: Okta Identity Engine consists of a sequence of steps to authenticate and authorize users. Identity Engine is the updated version of Okta Classic and is supported by Kolide.
- Okta Classic: Okta Classic is the first iteration of Okta SSO and the predecessor to Okta Identity Engine. Kolide does not integrate with this version.
- Okta Verify: Okta Verify is an MFA (multi-factor authentication) mobile app that is compatible with both version of Okta, although with significant improvements in Okta Identity Engine.
- Okta FastPass: Okta FastPass allows users to sign into Okta without using a password, and essentially adds FIDO2 auth to Okta Verify. With FastPass, users are generally authenticated through their device’s biometrics. FastPass cannot be used without Okta Verify.
- For those using Okta Fastpass, Okta offers some basic device based conditional access abilities, but it’s primarily concerned with verifying user identity. Kolide’s role is to complement it by running a robust series of checks on every device.
Kolide and Okta Factor Sequencing Options
There are several authentication methods available with Okta + Kolide today, all of which employ Kolide as a possession factor:
- Classic 2FA - Okta Password + Kolide
- Passwordless - FIDO2 + Kolide
- 3FA - Okta Password + Kolide + Biometric/Posession Factor (Multiple options, including Okta Verify and YubiKey)
If you’d like a look at what some of these factor sequencing setups look like in action, we’ve created videos that go through the steps for the following options:
For a more detailed guide to factor sequencing, check out our documentation page.
Regardless of the authentication methods used for Device Trust, the overall process flow works similarly.
- When a Kolide user initiates the authentication process after signing into Okta, a signed SAML request is sent from Okta to Kolide.
- After this request is sent, Kolide validates it and checks in with the Kolide agent installed on the device.
- Kolide then runs its checks against the user’s device to determine if there are currently any blocking issues.
- If blocking issues exist, the user is required to fix them before finishing the authentication process.
- After this process is complete, a signed SAML response is sent back to Okta from Kolide. Okta then validates the response and authenticates the user.
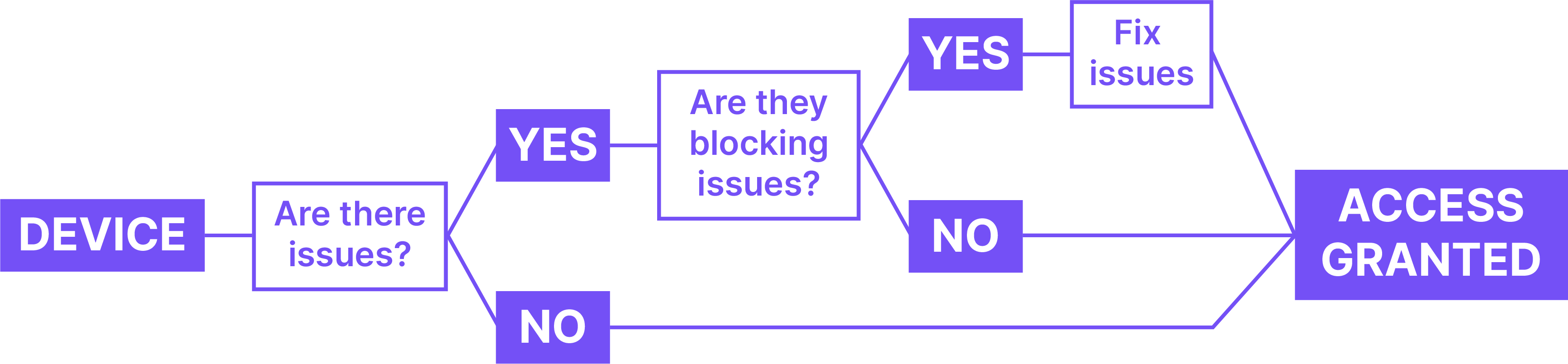
Not all issues trigger an immediate block. IT can determine how long the grace period should be before users are blocked, depending on an issue’s level of urgency.
The New Menubar App
It’s important to understand that while Kolide’s SSO integration is central to our product, it’s not the only way users interact with us. After all, we wanted to make Kolide part of authentication and block non-compliant devices, but we didn’t want to create any needless friction (or unpleasant surprises) for users.
So, hand-in-hand with our Okta integration, we created an app that alerts users to blocking issues as soon as we detect them. That way, a user never learns that their device has an issue when they’re trying to log in for an important meeting.
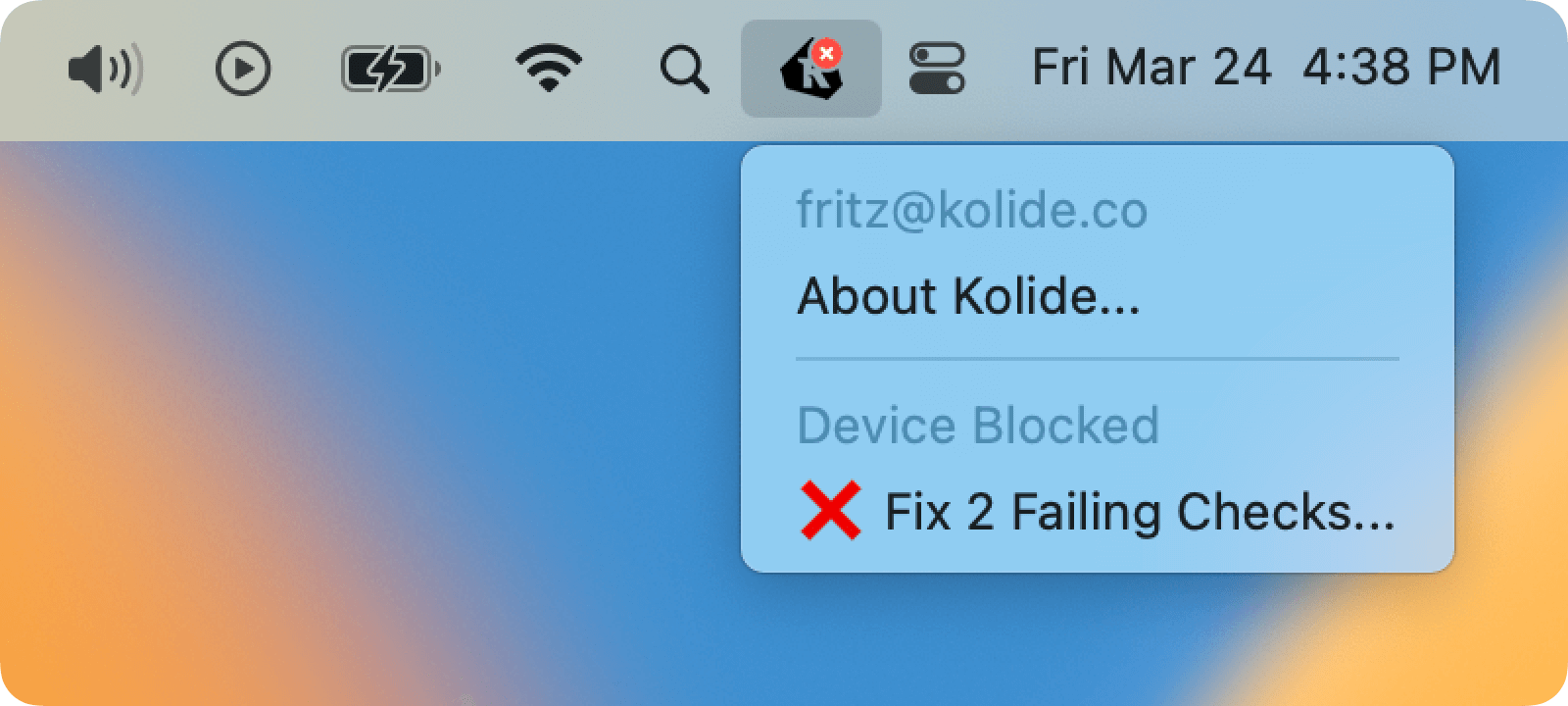
The new menubar application directly integrates with the new desktop app, and allows users to check their device for issues, see how long they have to resolve them, and navigate to the privacy center with just one click.
Kolide’s Mobile App
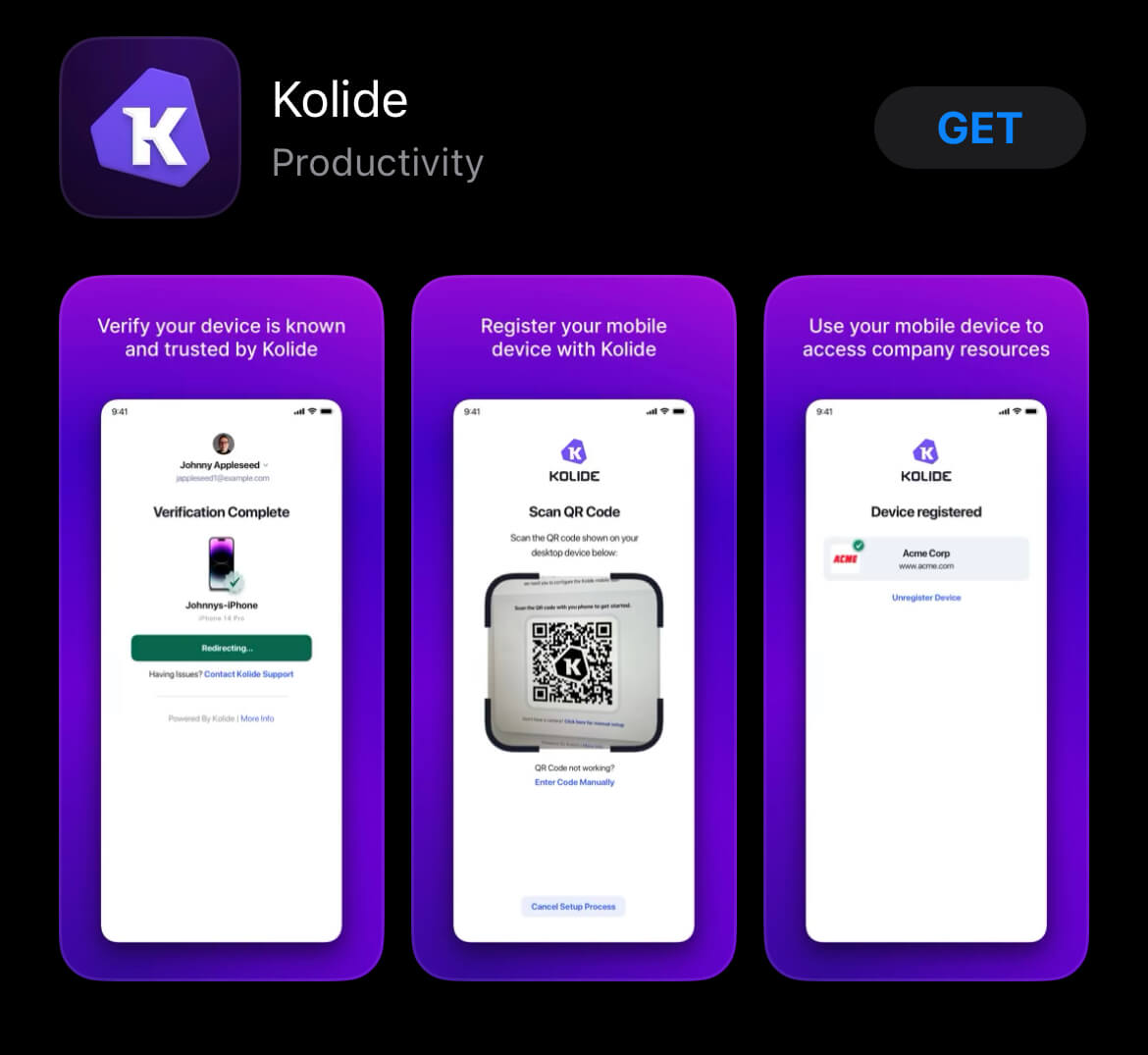
These days, end users aren’t just accessing sensitive data on their laptops and desktops, so along with our Okta integration, we’re also launching a new mobile app for iOS and Android.
What’s Next?
If you have Okta and are interested in Kolide, please get in touch with us so we can show you a demo and get you started.
Don’t have Okta but want to stay in the loop as we add more SSO providers? Subscribe to our newsletter!




