How to List Kernel Extensions Across All Macs
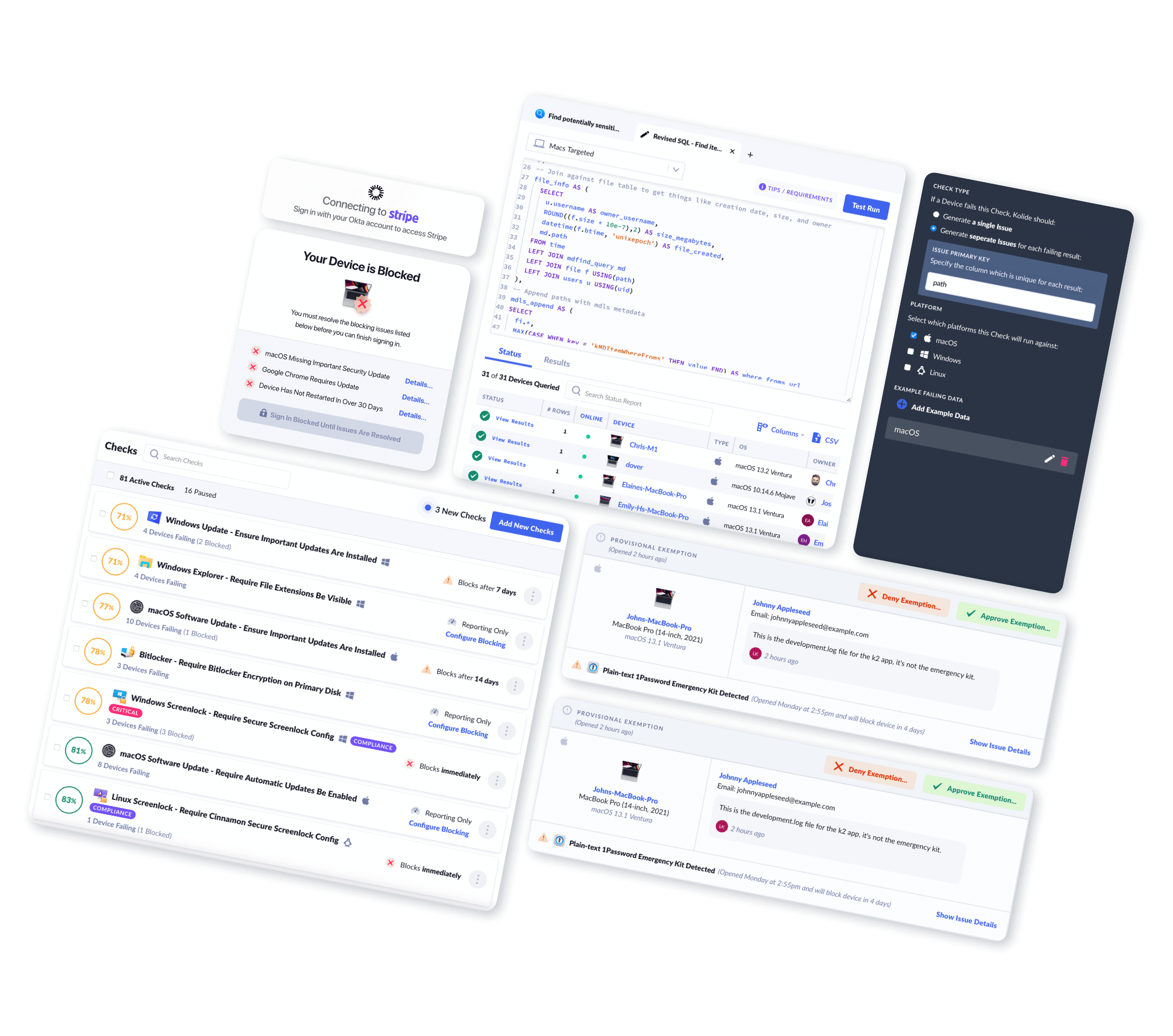
Using Kolide, you can easily view and query Mac Kernel Extensions across your fleet.
Introduction
Kernel extensions are utilized by macOS to extend the base kernel of a device. These extensions can be installed by the operating system or by a third party.
In versions of macOS 10.15 or earlier, certain user-installed software relied on special extensions to the system kernel. These kernel extensions allowed increased access to various OS subsystems and functionality that could not be obtained through standard installation means, but could impact system stability and performance.
Apple has the following to say with regards to stability:
Important: Kexts are no longer recommended for macOS. Kexts risk the integrity and reliability of the operating system, and users should prefer solutions that don’t require extending the kernel.
These kernel extensions can be reviewed by an end-user on a Mac using System Report by doing the following:
- Click the Apple menu at the top left of your screen
- Click About this Mac in the dropdown
- On the Overview tab, click the button labeled 'System Report…'
- In the System Report window, in the sidebar on the left, scroll down to Software > Extensions
For more information on kernel extensions please refer to the official Apple Support documentation: Kernel extensions in macOS
What Mac Kernel Extension Data Can Kolide Collect?
Kolide's endpoint agent bundles in osquery to efficiently collect Mac Kernel Extensions from Macs in your fleet. Once collected, Kolide will parse, clean up, and centrally store this data in Inventory for your team to view, query, or export via API.
Kolide meticulously documents every piece of data returned so you can understand the results.
Mac Kernel Extensions Schema
| Column | Type | Description | |
|---|---|---|---|
| id | Primary Key |
Unique identifier for the object |
|
| device_id | Foreign Key |
Device associated with the entry |
|
| device_name | Text |
Display name of the device associated with the entry |
|
| idx | Text |
Kernel extension load tag or index |
|
| linked_against | Text |
Indexes of extensions this Kernel extension is linked against |
|
| name | Text |
Kernel Extension label |
|
| path | Text |
Optional path to extension bundle |
|
| signature_authority | Text |
Certificate Common Name for signature |
|
| signature_cdhash | Text |
Hash of the Kernel Extension contents |
|
| signature_identifier | Text |
The signing identifier sealed into the signature |
|
| signature_team_identifier | Text |
The team signing identifier sealed into the signature |
|
| signed | Boolean |
|
|
| version | Text |
The text representation of the version |
|
| version_major | Bigint |
|
|
| version_minor | Bigint |
|
|
| version_patch | Bigint |
|
|
| version_subpatch | Bigint |
|
|
| version_pre | Text |
|
|
| version_build | Text |
|
|
| collected_at | Timestamp |
Time the row of data was first collected in the database |
|
| updated_at | Timestamp |
Time the row of data was last changed in the database |
|
What Can You Do With This Information?
Kolide enables you to write your own queries against the data the agent collects. This allows you to build your own reports and API endpoints. For example, you can:
SELECT
device_name,
signed AS kext_signed,
name AS kext_name,
version AS kext_version
FROM mac_kernel_extensions
WHERE name ILIKE '%fakesmc%'
OR name ILIKE '%virtualsmc%'
OR name ILIKE '%rehabman%'; | device_name | kext_name | kext_signed | kext_version |
|---|---|---|---|
| Chris-Hackintosh | org.netkas.driver.FakeSMC | 0 | 1800 |
| macOS-debug-build | com.rehabman.driver.USBInjectAll | 0 | 0.6.3 |
| Jerrys-iMax | org.netkas.driver.FakeSMC | 0 | 1800 |
| it-sec | org.netkas.driver.FakeSMC | 0 | 1800 |
| it-sec | com.rehabman.driver.USBInjectAll | 0 | 0.6.3 |
Why Should I Collect Mac Kernel Extensions?
End-User Privacy Consideration
Kolide practices Honest Security. We believe that data should be collected from end-user devices transparently and with privacy in mind.
When you use Kolide to list Mac Kernel Extension data from end-user devices, Kolide gives the people using those devices insight into exactly what data is collected, the privacy implications, and who on the IT team can see the data. This all happens in our end-user privacy center which can be accessed directly by employees.