How to Find Non-Genuine Windows Installations and Activate Them
Non-Genuine Windows is highly correlated with malware infection and the presence of other pirated software.
What is a Genuine Microsoft Product?
Shortly after introducing Windows XP in 2001, Microsoft faced unprecedented levels of piracy of its operating system. To combat this, they created an anti-infringement system named Windows Genuine Advantage (WGA) which they launched in 2006.
At its core, Genuine Advantage further extended the anti-piracy protections beyond entering and validating license keys during setup (a process known as activation). These extensions included continuous license validity checks that phoned home to Microsoft and visible consequences if Windows was found not to be genuine.
Why is There Non-Genuine Microsoft Software On My Devices?
There are many reasons non-genuine software may be installed on your PCs. In practice, these are the most common:
Intentional Piracy
End-users who are used to pirating software on their personal devices may be willing to take the same risk on their work devices, especially in situations where they are forced to use an outdated version of Windows.
This is a worst-case scenario because pirated software is often strongly correlated with malware infections which can compromise the integrity of the entire operating system.
In a 2017 IDC study commissioned by Microsoft, IDC found that one in three unlicensed or pirated copies of PC software caused malware infection.1
Developer Virtual Machines / Test Devices
macOS and Linux are quickly growing in market share among the preferred platforms for software engineers to use on their work devices. That being said, these developers often need to test cross-platform code on Windows to ensure compatibility. To do this, developers will use a virtual machine (VM) that runs Windows which they can boot-up on demand. When a VM isn’t practical—like on Macs running Apple silicon— older Intel Macs that can run Bootcamp may be used for the same purpose.
Developers often download pre-packaged VM images or ISOs from Microsoft that contain evaluation versions of Microsoft Windows. These images get the developer up and running, but within a few weeks begin prompting the developer to enter a valid license key. Since most developers don’t have the ability to instantly procure this software (and they don’t see the value) these ad-hoc installations quickly expire and are then considered non-genuine by Microsoft.
It’s important to identify these devices. While they aren’t used often, they still likely have sensitive files on them (like source code being tested and infrastructure secrets). In the case of VM they may even have the ability to access the files or the network available to the host system. These all represent potential risk on a device that isn’t being managed as if it is a real asset.
Malware Infections
Unrelated to piracy, poorly engineered malware can cause a previously licensed and genuine version of Windows to suddenly report as non-genuine. This occurs because the malware, in an effort to compromise the system, corrupts core services and important files on the PC that are associated with the Genuine Advantage capability.
This occurs when malware is attempting to hook deeply into the system (ex: a rootkit) so it can undermine the integrity of the built-in security of Windows and hide an infection from the end-user.
Chasing down non-genuine Windows installations can be the first thread in finding a significant dormant infection, allowing you to correct it, before it becomes a serious problem.
Programmatically Locating Non-Genuine Versions of Windows
Microsoft WMI enables you to enumerate the state of Windows License using the
SoftwareLicensingProduct table (docs).
SELECT
Name, GenuineStatus, LicenseStatus, PartialProductKey
FROM SoftwareLicensingProduct
WHERE
PartialProductKey IS NOT NULL AND
Name LIKE "Windows%" AND
(LicenseStatus != 1 OR GenuineStatus = 1);
You can run this query right from the Windows Terminal using the
Get-WMIObject PowerShell cmdlet.
Get-WMIObject -Query 'SELECT Name, GenuineStatus, LicenseStatus, PartialProductKey FROM SoftwareLicensingProduct WHERE PartialProductKey IS NOT NULL AND Name LIKE "Windows%" AND (LicenseStatus != 1 OR GenuineStatus = 1);';
Why Is Non-Genuine Microsoft Software a Problem?
It can be tempting for IT staff to want to avoid turning over the software licensing rock. Once they become aware of it, they now have to solve a tricky and expensive problem that only serves to benefit Microsoft financially.
While it’s easy to empathize with this viewpoint, looking at the facts, the benefits of having this visibility to you and your organization far outweigh the perceived (and often unrealized) negative impacts.
As stated above, unlicensed or counterfeit versions of Windows are indicators of other potential problems. For example:
Windows PCs with non-genuine software are much more likely to be compromised by malware.
Windows PCs with non-genuine software are more likely to be un-managed or generally unknown to the IT Team.
Windows PCs that are non-genuine may indicate a developer use-case that isn’t being accounted for by the organization in any official way.
These insights are extremely valuable and well worth the effort of enumerating non-genuine Windows installations.
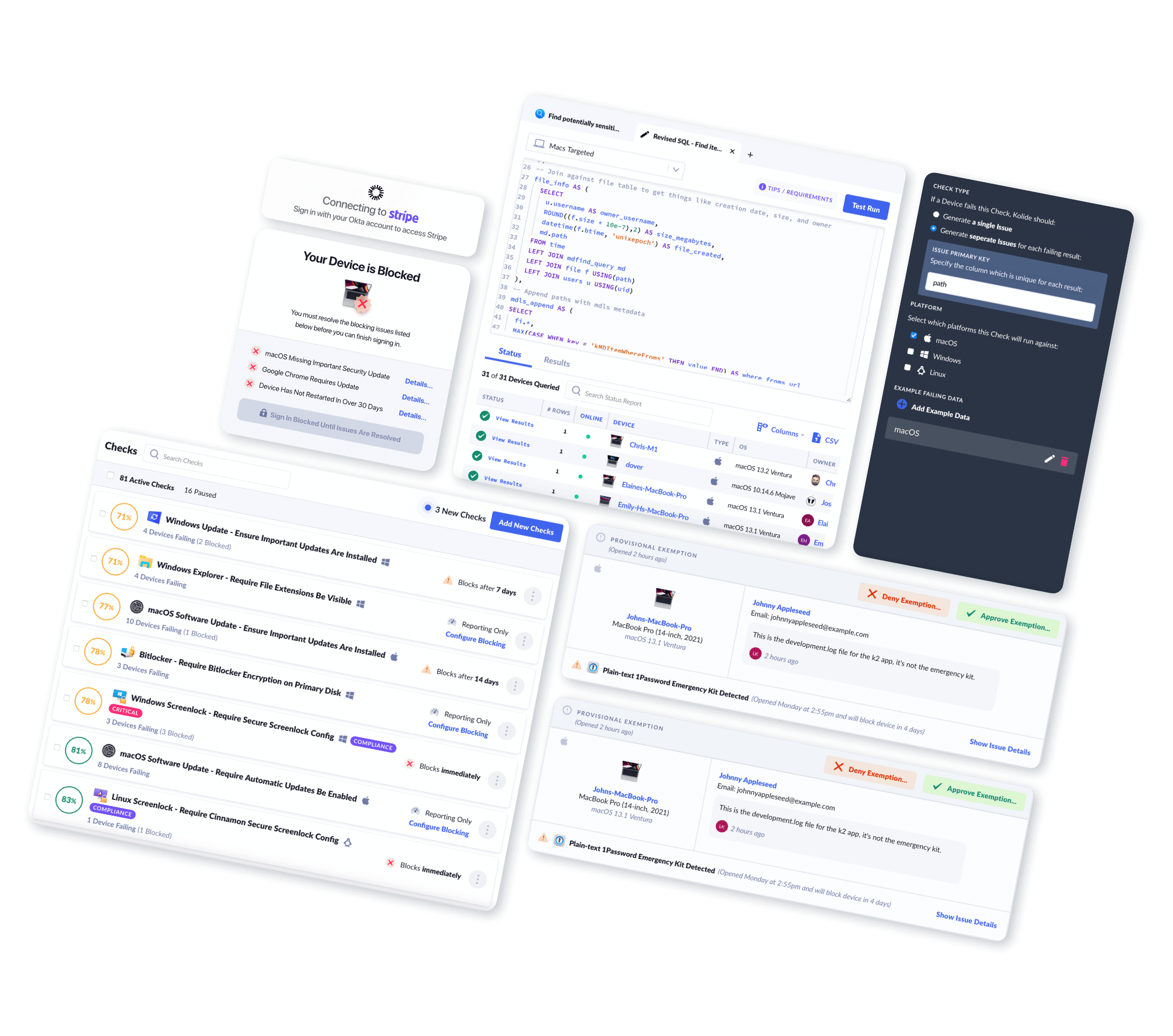
How Does Kolide’s Detection Work?
Kolide’s endpoint agent is capable of running queries against WMI so you can aggregate Microsoft License information across all of your Windows PCs.
How Does Kolide Remediate This Problem?
This problem cannot be remediated through traditional automation with tools like an MDM. You need to be able to stop devices that fail this check form authenticating to your SaaS apps and then give end-users precise instructions on how to unblock their device.
Kolide's Okta Integration does exactly that. Onece integrated in your sign-in flow, Kolide will automatically associate devices with your users' Okta identities. From there, it can block any device that exhibits this problem and then provide the user, step-by-step instructions on how to fix it. Once fixed, Kolide immediately unblocks their device. Watch a demo to find out more.